
Security Rule overhaul, Privacy Rule changes, mandatory risk assessments, new technical safeguards, and enforcement trends, everything covered entities and business associates need to act on now.
⚡ Quick Answer - Featured Snippet Ready What are the major HIPAA changes in 2026?The major HIPAA changes in 2026 include: (1) a sweeping HIPAA Security Rule overhaul expected to be finalized in May 2026, (2) mandatory multi-factor authentication (MFA) and full ePHI encryption becoming required not merely "addressable," (3) annual security risk assessments now explicitly required, (4) 24-hour breach reporting obligations for business associates, (5) updated Notices of Privacy Practices (NPPs) required by February 16, 2026, and (6) expanded OCR enforcement targeting risk analysis and risk management failures. |
|---|
Why 2026 Is the Most Critical Year for HIPAA Compliance Since 2003
HIPAA is undergoing its most sweeping transformation in over two decades. The original HIPAA Security Rule was introduced in 2003. Apart from a meaningful update in 2013 with the HIPAA Omnibus Rule, the framework remained relatively static even as ransomware, cloud computing, and AI fundamentally changed the healthcare data landscape.
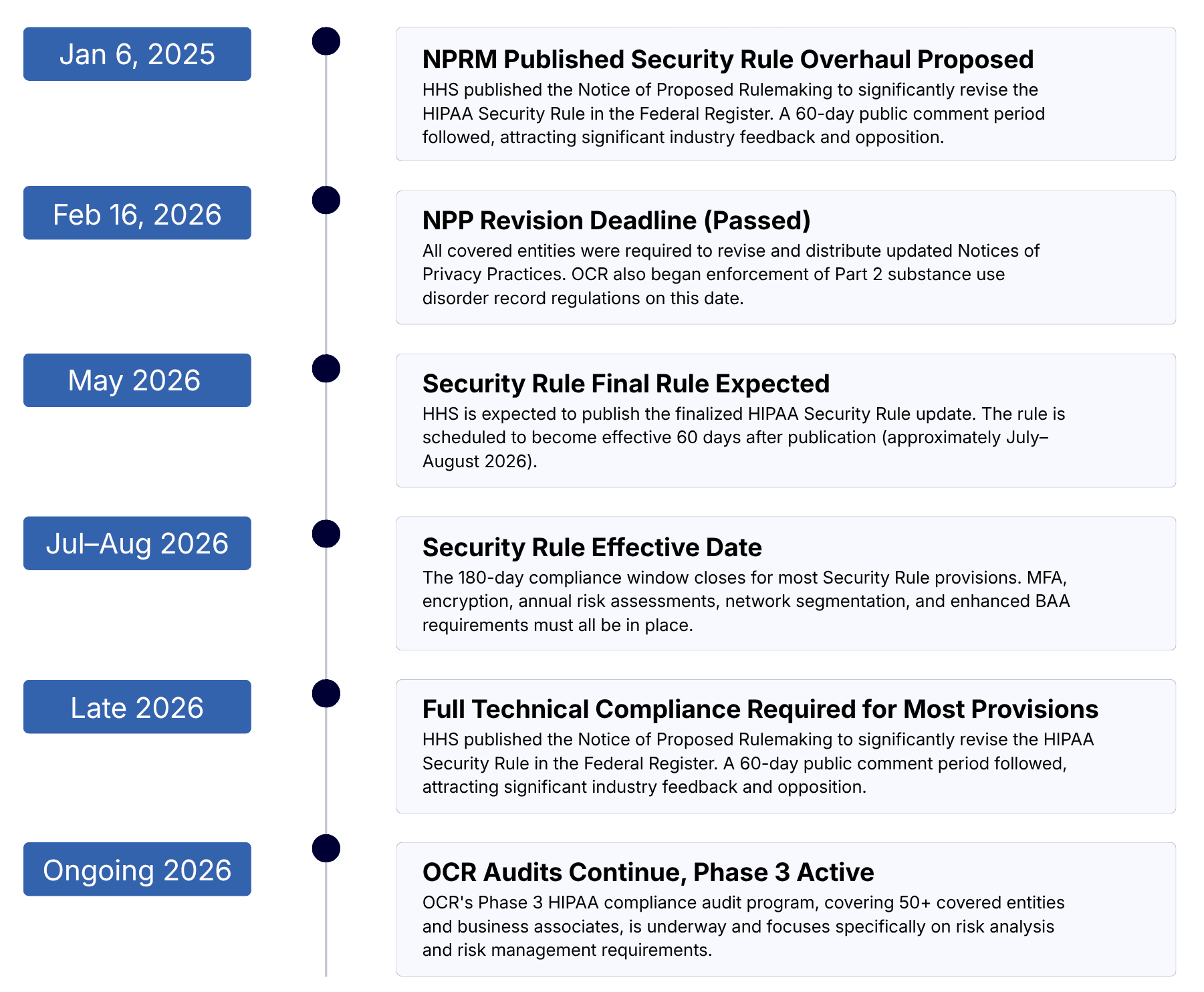
In 2026, that era of relative stability ends. The U.S. Department of Health and Human Services (HHS) and its Office for Civil Rights (OCR) have signaled through a Notice of Proposed Rulemaking (NPRM) issued on January 6, 2025, and a series of aggressive enforcement actions that the age of HIPAA as a "policy exercise" is over. Compliance must now be technically enforced, continuously monitored, and measurably proven.
Covered Entities:
All healthcare providers, health plans, and healthcare clearinghouses that transmit health information electronically must comply.
Business Associates:
Third-party vendors, cloud providers, billing services, and IT companies that handle ePHI face expanded direct obligations in 2026.
OCR Enforcement Record:
OCR closed 2025 with 21 settlements and civil monetary penalties the second-highest annual total on record, signaling no slowdown.
Maximum 2026 Penalty:
HIPAA violation penalties in 2026 reach up to $2,134,831 per violation category for willful neglect, adjusted for inflation.
⚠️ Key Stat In 2025, OCR levied over $6.6 million in HIPAA fines affecting covered entities and business associates ranging from small physician practices to large health systems. Every organization is a target. |
HIPAA Security Rule 2026 Overhaul: What's Actually Changing
The HIPAA Security Rule governs how covered entities and business associates must protect electronic protected health information (ePHI). The proposed 2026 revision published in the Federal Register on January 6, 2025, and expected to be finalized in May 2026 represents the most significant update since the rule's original adoption.
"Security is no longer about documenting intent it's about proving technical enforcement."
- HHS Office for Civil Rights, 2026 Regulatory Agenda
1. Elimination of "Addressable" vs. "Required" Safeguards
The single largest change in the proposed rule is the elimination of the distinction between "required" and "addressable" safeguards. Under the current rule, "addressable" controls gave organizations flexibility they could evaluate whether implementing a safeguard was reasonable and appropriate, and document why an alternative measure sufficed. That flexibility ends under the new rule. Nearly all implementation specifications become mandatory, with only limited, explicitly defined exceptions. This directly closes gaps that OCR found contributed to the rise in ransomware attacks and large-scale healthcare data breaches.
2. Mandatory Multi-Factor Authentication (MFA)
MFA will be required for all system access to ePHI not just remote access. This means any clinician, administrator, or IT personnel accessing patient records must authenticate through at least two independent verification factors. Organizations cannot "opt out" by documenting an alternative control.
3. Mandatory Encryption of ePHI
Encryption transitions from an "addressable" standard to a fully required control both at rest and in transit. Any system handling ePHI must encrypt that data without exception. The "document your reasoning for not encrypting" workaround that some smaller organizations relied upon is no longer available.
4. Annual Compliance Audits & Technical Testing
Covered entities must now conduct formal compliance audits at least once every 12 months. Additionally, the proposed rule specifies required technical testing frequencies including vulnerability scanning and penetration testing that must be conducted by qualified cybersecurity professionals. Written records of findings and corrective actions must be maintained.
5. Network Segmentation
Electronic health record systems must not share networks with non-clinical connected devices such as CCTV cameras or IoT systems. Network segmentation becomes a formal compliance requirement, reducing the attack surface for lateral movement during a breach.
6. Technology Asset Inventories
Organizations must maintain comprehensive asset and data inventories documenting all systems, software, and devices that create, receive, maintain, or transmit ePHI. These inventories must be updated at least annually or after significant environmental or operational changes.
7. One Hour Access Revocation
Organizations must be able to revoke ePHI system access within one hour of employee termination. Ad-hoc offboarding processes are no longer acceptable under the proposed compliance framework.
📌 Implementation Timeline The Security Rule update is expected to be effective 60 days after publication (approximately July–August 2026), with most provisions requiring compliance within 180 days. This places the hard compliance deadline in late 2026 or early 2027. Organizations with significant gaps should begin remediation immediately. |
HIPAA Privacy Rule Updates: What Changed and What's Coming
he HIPAA Privacy Rule governs how protected health information (PHI) can be used and disclosed. Two major Privacy Rule developments have reshaped the compliance landscape heading into 2026.
Notices of Privacy Practices (NPP) Deadline: February 16, 2026
All covered entities were required to revise their Notices of Privacy Practices (NPPs) by February 16, 2026. The new NPPs must clearly explain to patients how their personal information is protected, what their rights are, and how sensitive health information is handled. Organizations that missed this deadline are now in violation and exposed to OCR enforcement.
🚨 Deadline Already Passed The February 16, 2026 NPP revision deadline has passed. If your organization has not updated its Notice of Privacy Practices, this is an active compliance deficiency. Review your NPPs against the requirements at 45 CFR § 164.520 immediately. |
|---|
Reproductive Health Data Protections Complex Legal Landscape
In April 2024, HHS finalized updates to the HIPAA Privacy Rule that prohibited the use or disclosure of PHI to investigate or penalize individuals for obtaining or providing lawful reproductive health services. However, on June 18, 2025, the U.S. District Court for the Northern District of Texas vacated most of this rule. The court preserved certain NPP modifications at 45 CFR § 164.520, which remain in effect. Healthcare organizations should consult legal counsel on their specific obligations given the shifting regulatory environment in this area.
Part 2 / Substance Use Disorder Records Alignment
A Final Rule published February 8, 2024 aligned 42 CFR Part 2 (governing substance use disorder treatment records) more closely with HIPAA. Full compliance with these changes was required by February 16, 2026. OCR now has expanded authority to enforce Part 2 regulations, which it began exercising on that date.
HIPAA Risk Assessments 2026: Annual, Actionable, and Audit-Ready
The HIPAA security risk assessment formally required under 45 CFR § 164.308(a)(1) is the single most cited deficiency in OCR enforcement actions. And in 2026, the bar has been raised significantly. OCR launched a dedicated Risk Analysis Enforcement Initiative that remains intensely active, and the current OCR Director Paula M. Stannard has publicly confirmed that the initiative will expand in 2026 to encompass risk management not just risk analysis.
What a Compliant 2026 Risk Assessment Must Include:
A compliant HIPAA risk assessment is not a checkbox exercise. Under both current requirements and the proposed 2026 updates, a thorough risk assessment must:
ePHI Inventory:
Identify all systems, devices, and locations where ePHI is created, received, maintained, or transmitted including cloud storage, mobile devices, and third-party integrations.
Threat & Vulnerability Identification:
Document all reasonably anticipated threats to ePHI confidentiality, integrity, and availability including ransomware, insider threats, and configuration errors.
Likelihood & Impact Ratings
Assign quantified likelihood and impact scores to each identified risk, producing a prioritized risk matrix that drives remediation decisions.
Documented Remediation Plan:
Create a formal risk management plan that reduces identified risks to an acceptable level and document that it has been executed. Documentation without action will fail audits.
Annual Frequency - Now Explicit
The current rule does not specify how often risk assessments must be conducted, and many organizations have exploited this ambiguity to avoid regular assessments. The proposed 2026 Security Rule eliminates that ambiguity entirely: risk assessments must be conducted at least annually, and whenever significant changes occur to the organization's technology, operations, or regulatory environment.
✅ Best Practice Recommendation Align your HIPAA risk assessment with the NIST Cybersecurity Framework or use the HHS Security Risk Assessment (SRA) Tool. Organizations that have implemented recognized security practices for at least 12 months prior to a violation may receive reduced penalties under the HIPAA Safe Harbor Law. |
|---|
Enforcement Actions for Inadequate Risk Analysis (Recent Examples)
Organization | Settlement Amount | Core Deficiency |
|---|---|---|
Premera Blue Cross | $6.85 million | Insufficient risk assessment contributing to a breach affecting 10.4 million individuals |
Advocate Health Care Network | $5.55 million | Failure to conduct an enterprise-wide risk assessment |
Banner Health | $1.25 million | Failure to conduct an accurate risk analysis covering all ePHI |
North Memorial Health Care | $1.55 million | No risk assessment and no BAA with a major contractor |
Unnamed entity (ransomware) | $90,000 | No risk analysis conducted; ransomware attack affected 14,273 patients |
New HIPAA Safeguards 2026: From Addressable to Mandatory
The shift from "addressable" to "required" safeguards is the defining technical change of the 2026 HIPAA Security Rule update. Below is a summary of the key new mandatory controls that healthcare organizations must implement.
Multi-Factor Authentication:
Required for all ePHI system access onsite and remote. No exceptions based on organization size or role type.
Encryption (At Rest & In Transit):
Full encryption of ePHI on all systems servers, laptops, mobile devices, and data transmitted across any network.
Network Segmentation:
Clinical systems must be isolated from non-clinical devices (CCTV, IoT). Defined ePHI network perimeters are required.
Penetration Testing:
Annual penetration testing by qualified cybersecurity professionals, with written records of findings and corrective actions.
Rapid Access Revocation:
ePHI system access must be revoked within one hour of employee termination or role change.
Vulnerability Scanning:
Regular vulnerability scans at defined intervals, with enhanced frequency when risk assessments identify elevated threats.
Asset Inventory & Data Maps:
Documented network maps showing all ePHI flows, updated at least annually or after operational/environmental changes.
Incident Response Plans:
Formal incident response plans must be documented, implemented, and annually tested. Business associates must notify covered entities within 24 hours of plan activation.
❌ Documentation Alone Will Fail Audits OCR's 2026 audit standards require that controls be implemented, tested, and provable not merely documented in a policy. A signed BAA is no longer sufficient vendor accountability; covered entities must obtain annual written verification confirming business associates have implemented required technical safeguards. |
HIPAA 2026 Compliance Timeline: Key Dates to Know
HIPAA Violation Penalties 2026: Fines, Tiers, and Enforcement Priorities
HIPAA penalties are adjusted annually for inflation. The 2026 figures reflect the cost-of-living adjustment multiplier for 2025, published on January 28, 2026. The tiered civil penalty structure established by the HITECH Act determines fines based on the level of culpability.
Tier | Violation Type | Per-Violation Range (2026) | Annual Cap |
|---|---|---|---|
| Lack of knowledge - entity could not have reasonably known | $141 – $71,162 | $2,134,831 |
| Reasonable cause - should have known, no willful neglect | $1,424 – $71,162 | $2,134,831 |
| Willful neglect - violation corrected within required period | $14,232 – $71,162 | $2,134,831 |
| Willful neglect -violation not corrected | $71,162+ | $2,134,831 |
Criminal penalties (handled by the Department of Justice) can reach $250,000 and up to 10 years in prison for intentional misuse or sale of PHI. These apply to individuals not just organizations.
OCR 2026 Enforcement Priorities
OCR's enforcement agenda for 2026 focuses on three primary areas:
Risk Analysis Initiative
Expanding to include risk management OCR will verify that identified risks are actively managed and reduced to acceptable levels, not just documented.
Right of Access Initiative
Continued enforcement of patients' rights to access their medical records within 30 days. Over 50 financial penalties have been issued under this initiative since 2019.
Part 2 (SUD Records)
OCR now has delegated responsibility for enforcing 42 CFR Part 2 governing substance use disorder treatment records, effective February 16, 2026.
📢 Phase 3 HIPAA Audits Are Live OCR confirmed in March 2025 that Phase 3 of its HIPAA compliance audit program is underway, initially covering 50 covered entities and business associates. Audits focus on risk analysis and risk management requirements of the HIPAA Security Rule. |
|---|
Business Associate Requirements: New Accountability Standards
Approximately 40% of all HIPAA breaches involving 500+ records are attributable to business associates, according to OCR data yet many BAs still fail to conduct their own independent risk assessments. The 2026 Security Rule update directly addresses this gap with significantly expanded BA obligations.
Key new business associate requirements include:
Conduct their own independent annual HIPAA security risk assessments (not rely solely on covered entity assessments)
Notify covered entities within24 hoursof activating an incident response or contingency plan
Implement all required technical safeguards including MFA, encryption, and network segmentation without exception
Provide annualwritten verificationto covered entities confirming technical safeguards are in place (a signed BAA alone is no longer sufficient)
UpdateBusiness Associate Agreements (BAAs)to clearly define BA cybersecurity obligations aligned with the new Security Rule requirements
Maintain incident response plans and test them annually
Share written compliance testing results with covered entities
💡 BAA Update Action Required All Business Associate Agreements should be reviewed and updated before the Security Rule's compliance deadline. BAAs must now explicitly address cybersecurity obligations, incident reporting timelines, annual verification procedures, and contingency plan notification requirements. |
|---|
HIPAA Compliance Checklist 2026: 15 Priority Actions
Use this checklist to audit your organization's preparedness for HIPAA's 2026 requirements. This list is prioritized by regulatory urgency and enforcement risk.
Action | Details |
|---|---|
| Ensure updated Notices of Privacy Practices reflecting 2024 Privacy Rule changes are in place (deadline February 16, 2026, now past). |
| Document all ePHI locations, assess threats and vulnerabilities, assign likelihood/impact ratings, and produce a remediation plan. |
| Deploy MFA for all system access to ePHI, onsite and remote, across all users and roles. |
| Audit every system, device, and transmission channel for encryption status and remediate gaps immediately. |
| Evaluate current Security Rule compliance posture against the proposed 2026 requirements and identify gaps requiring remediation. |
| Revise all BAAs to include explicit cybersecurity obligations, 24-hour reporting requirements, and annual verification provisions. |
| Collect written confirmation from business associates that required technical safeguards are implemented and tested. |
| Separate clinical ePHI systems from non-clinical networks including IoT, CCTV, and guest Wi-Fi. |
| Document, implement, and annually test a formal incident response plan aligned with the proposed 2026 requirements. |
| Document all systems, devices, and applications that touch ePHI, and establish a process for keeping it current. |
| Engage qualified cybersecurity professionals to conduct penetration testing and maintain written records of findings and corrective actions. |
| Establish and test procedures to revoke ePHI access within one hour of employee termination. |
| Implementing recognized security practices for 12+ months may reduce penalties under the HIPAA Safe Harbor Law. |
| Provide HIPAA training on updated policies, breach response, privacy protections, and the consequences of unauthorized PHI access. |
| Keep policies, risk assessments, training records, BAAs, audit logs, and incident reports organized and accessible for potential OCR review. |
HIPAA compliance in 2026 is not a one-time task. It is an ongoing commitment that demands consistent effort, updated processes, and the right tools. With the Security Rule overhaul underway, OCR audits in full swing, and stricter business associate obligations now in effect, organizations that act early will be far better positioned to avoid penalties and protect patient trust. Whether you are just beginning your compliance journey or looking to strengthen an existing program, the steps outlined in this roadmap give you a clear, actionable path forward. Start with your risk assessment, close the gaps, and build a culture where compliance is not a burden but a baseline.